Housing is one of the key fundamentals for every household. Having the flexibility and availability of the right home will allow one to adjust comfortably when the family nucleus changes with time. Imagine a young couple that is planning for a family but is financially strapped and cannot afford a large home, obviously they will have to settle with a home that is smaller and more affordable. After a couple of years, their parents and children start to live with them. If they are more financially sound by then, the couple would need a place that is larger to accommodate a family of 7 people. The availability of homes in the market is key for the family of this size. 20 years down the road, the children would have grown up and moved out, and the family nucleus has strung back to just the couple living together. They will have the flexibility to downsize their home, or stay where they are currently residing.
In the same way, any device will need a housing to encapsulate the PCB. PCB design changes with time and with the demands and needs of the market, the PCB can become larger or smaller. A suitable electronic housing will need to provide the flexibility to adjust to the needs of the PCB and components.
Phoenix Contact offers a wide range of housing for our customers. From DIN-rail mounted, desk or wall mounted, to outdoor applications and handheld types.
For this blog, we would like to touch on the latest addition to our electronic housing family, the modular ICS housing system mounted on the DIN-rail that is for future-oriented automation devices.

What is so special about this product compared to other housing products that are available in the market? How is Phoenix Contact ICS modular housing unique from rest in the market?
Let’s start from the beginning, from the R&D standpoint.
Say today the R&D team needs to redesign a din rail mounted controller to be integrated with their new machine, they need to come up with the concept and proof of concept within 2 months. With Phoenix Contact ICS modular housing, we can fulfil their needs, taking into consideration of their demands of:
- Tight timeline
- Unique design required with their company logo
- Reasonable cost
Phoenix Contact has an online configurator that allows the customer to configure and select the right housing for their needs. The available options for the R&D engineers in our online configurator would consist of:
- Size of the housing to fit the size of the PCB.
- Single or twin PCB allowed in the housing.
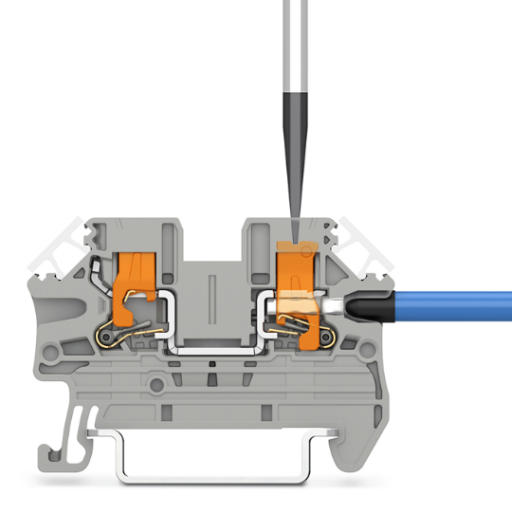
- Accessories options on the upper and lower side of the housing – such as connectors, heatsink & fillers with vent, USB, RJ45, D-sub or antenna.
- If customer has any customise cut out required, we can do it accordingly with our existing fillers.
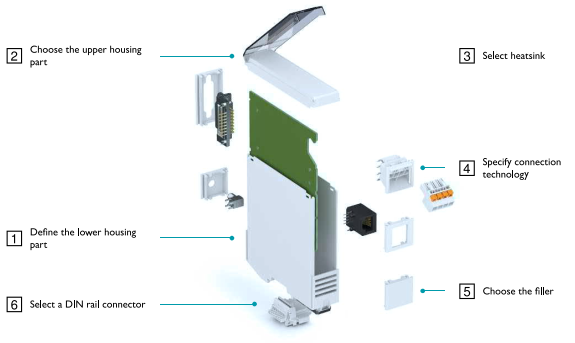
- T-bus connector available for the requirement of additional I/O modules.
- Front cover design options: Hinged transparent cover, flat closed cover or individualised custom cover. Customised printing and cut outs are also available for a nominal fee.
No additional tooling charges involved!

- 3D simulation and CAD files available for download together with the part numbers of all selected parts and accessories.
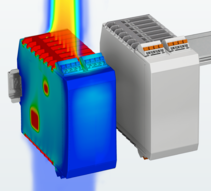
- Heat simulation available if used for IC or electronic components that generate lots of heat.
While many other companies charge for the thermal simulation, these are all freely available online!
Only Phoenix Contact provide such extensive product offerings and services which translate to:
- Cost effectiveness – No tooling fee on a new housing design with the advantage of our semi-customisable housing and free thermal simulation.
- Unique housing designed by the customer – Custom housing with printing and individualised covers.
- Quick sample service – samples can be requested online or through an email to the local representative.
- Future-proof and full proof design – Engineers can switch to the same series of housing with different sizes for future designs and Phoenix Contact will constantly be adding more accessories and services to value-add to the customers.
After all the designs are completed, engineers will need to transfer the information to their purchasing team and prepare for mass production. From the online configurator, you can download the part numbers of every piece part in an excel spreadsheet. This will seamlessly translate the information from the R&D team to the purchaser with extensive information in terms of:
- Drawings
- Pricing
- Piece parts and manufacturing part numbers
- One supplier for the fully established housing requirements from material, printing, and customisation.
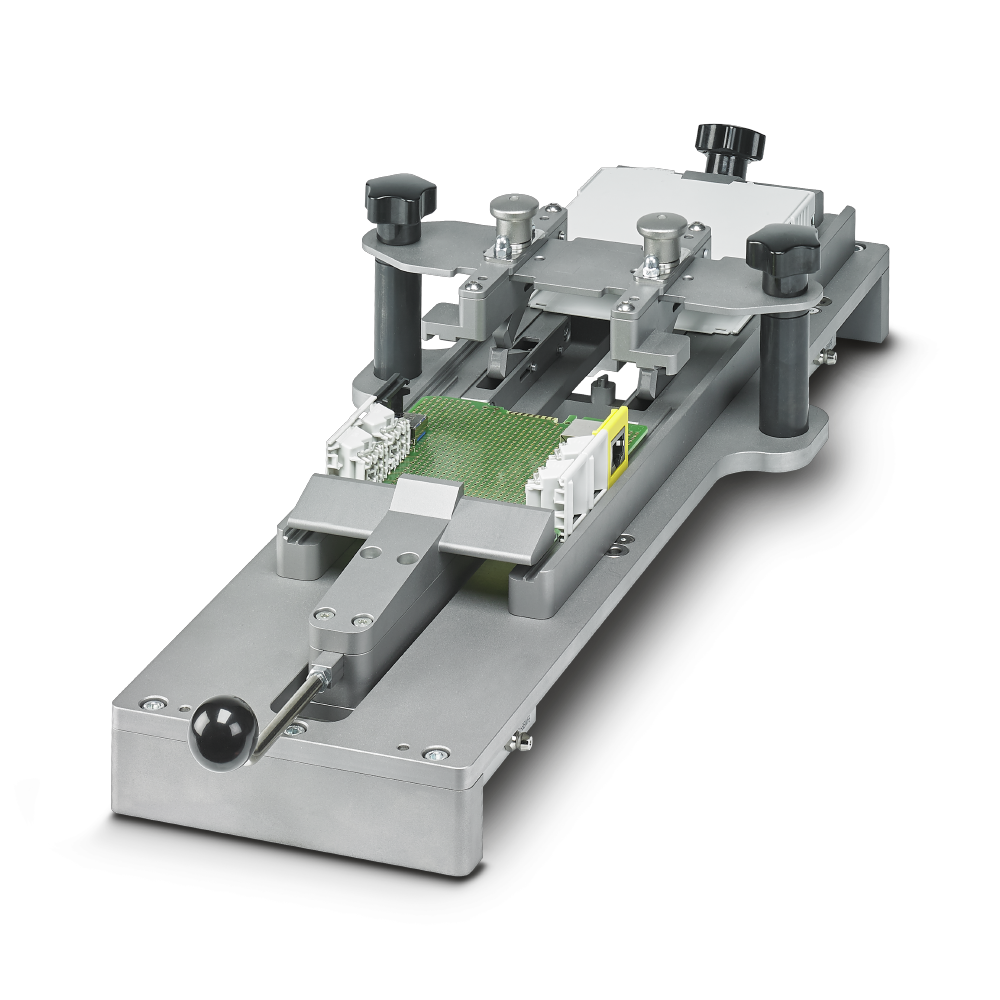
A well-thought-out product, the ease of the production process cannot be neglected. Phoenix Contact has designed a mounting device that is able to assemble all the different housing configurations, and shorten the assembly process to mere seconds. That is both innovation and cost saving. To find out more about the mounting device and the operation, see this link.
Reach out your local Phoenix Contact sales team to find out how we can help launch our new projects effective and efficiently.
Looking forward to hearing from you soon.